Back to manifestations
System Design // 2025
Cyber Protocol
Security through Elegance
Next.jsTailwind v4Lucide IconsLenis
Source_Verified // 2026.Archive
01_The_Challenge
Cyber Protocol, a cybersecurity firm, suffered from the 'boring security' stereotype. They needed to look elite, untouchable, yet modern.
02_The_Evolution
Built an encrypted-theme interface using mono-spaced typography and holographic shaders. The UI behaves like a high-end terminal, emphasizing the 'Elite Intelligence' they provide.
Neural_Analysis_Protocol
Intelligence Deep-Dive
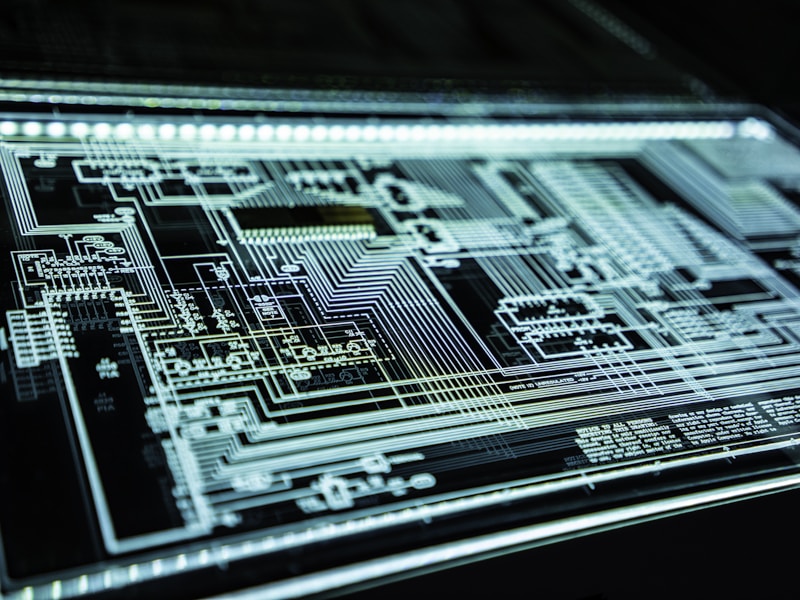
The Architecture of Logic
Synchronizing technical specifications for this release. Every line of code is measured for optimal performance and structural integrity.
Performance_Index98.4%
Computational_DepthAdvanced
// INITIALIZING_REPRODUCTION_PROTOCOL...
// LOADING_ASSETS: COMPLETED
// RUNNING_DIFF_ANALYSIS: NO_ERRORS
// OPTIMIZING_VIEWPORT_SCALING...